We're thrilled to announce that Zebrium has been acquired by ScienceLogic!
Learn MoreWe're thrilled to announce that Zebrium has been acquired by ScienceLogic!
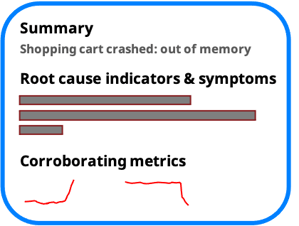
Learn MoreWhen you know there's a problem, automatically see its root cause in the Zebrium portal or inside your incident management tool.
![]()
Zebrium is always looking problems by scanning for anomalous patterns in your logs. You can use these to proactively catch incidents that aren't detected by other tools.
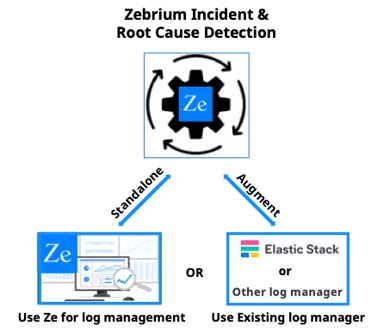
Augment your log manager - Use your existing log manager for dashboarding and search, and let Zebrium automatically find root cause when you are troubleshooting a problem.
Use with the Elastic Stack - With ZELK Stack, logs are sent to Zebrium using a Logstash output plugin. and root cause reports are sent back to Elasticsearch for viewing directly inside Kibana.
Zebrium standalone - Automatically see the core set of log events that explain the problem or zoom out to see an aggregated view of surrounding related error and anomaly events. You can also "peek" into any log stream to see what else is going on.
.png?width=269&name=Zebrium%20is%20SOC%202%20Type%201%20Certified%20(1).png)
Zebrium adheres to industry best practices for security including: SOC 2 Type 1 certification, encryption of data in flight, AES-256 encryption of data at rest, granular removal of sensitive records or fields, secure isolation of customer data and an option for a dedicated instance and VPC. All customer data will be deleted upon termination of service or upon request. For customers with the most stringent security requirements, there is also an on premises version. Read our security policy here.
Get started in just a few minutes by installing our log collector or using a Logstash output plugin. For best results, please induce an app failure or you won't be able to experience automated root cause analysis. If you can't do that, try it with a sample microservices demo app.
Privacy Policy Terms of Service Cookie Settings © 2022 by Zebrium, Inc.